Sometimes it is necessary to intervene in the Production System to correct an extremely urgent problem. That is to perform an action which is not normally done.
What are we supposed to do in these situations? Do we really need specific tools or we can carry out what is required in a safe and secure way?
Read More
Topics:
sicurezza sap,
sap super user,
sap consulenza security,
super utenti sap,
emergency users
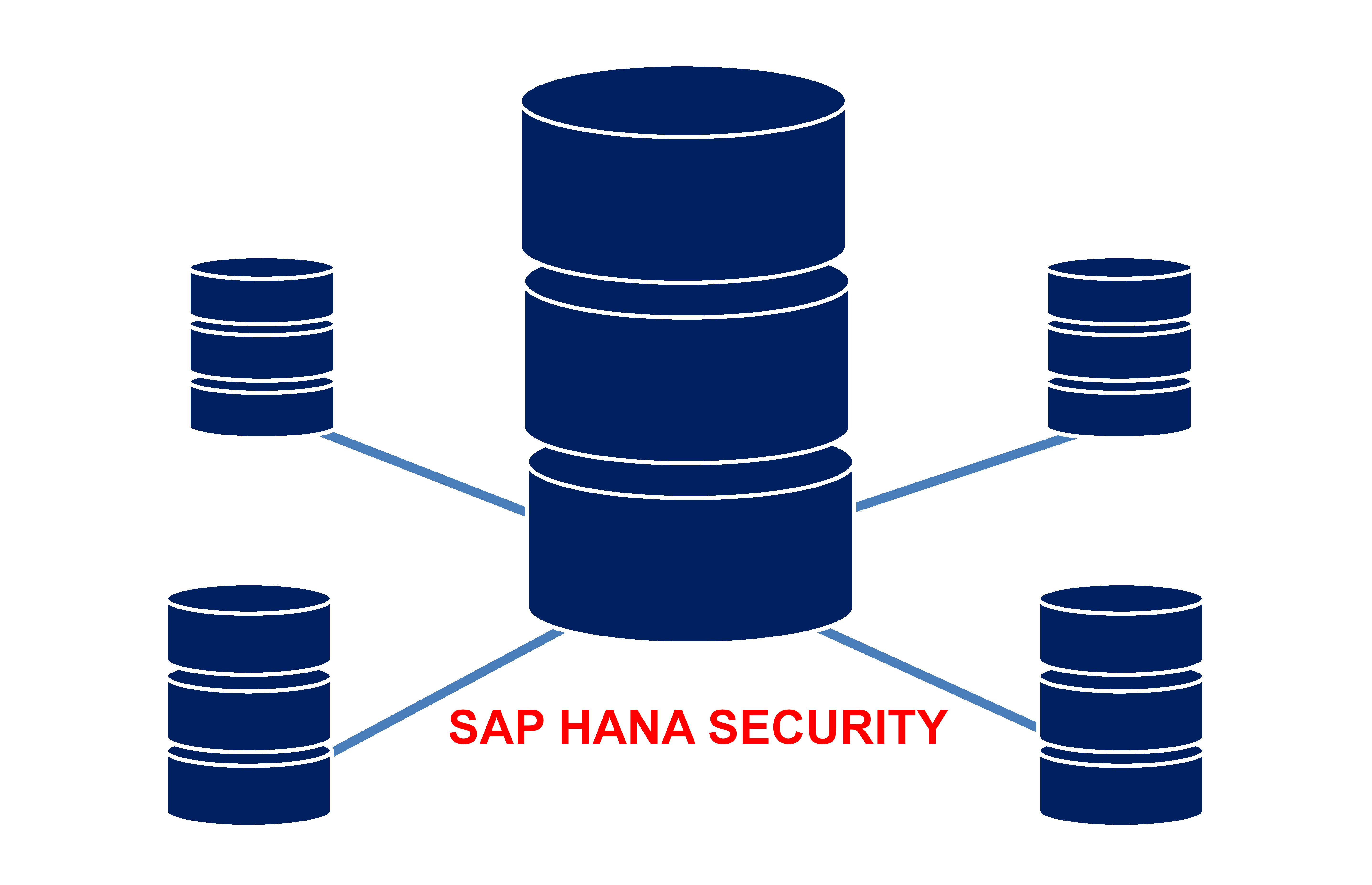
Have you replaced the database with SAP HANA? There are several new Security features to activate!
Enable all features for SAP HANA Security! Follow the tips to protect data and ensure database compliance.
Read More
Topics:
auditing,
SAP Security,
sap hana
Data retrieval is normal in a management system. But what are the tools available in a SAP ERP system? Is it correct reporting in a transactional system?
What are the security impacts in doing corporate data reporting in SAP and how can they be mitigated? What is the SAP query survival manual?
Read More
Topics:
sap consulenza security,
sap query,
governance,
tabelle,
sicurezza dei dati sap
Currently, there is no one-size-fits-all solution to address all the issues required by the GDPR.
SAP proposes different systems, see what they are and what they are used for. SAP offers different systems: what are those and what are they for?
Read More
Topics:
sap data masking,
data privacy,
SAP GDPR,
sap ilm gdpr,
sap tdms
Having within the company’s awareness also on the part of SAP developments is certainly important. Especially in order not to be dependent on third parties even for simple problems.
We don’t talk about ABAP developers directly. But what are or could be the impacts in having an internal group of developers for the security aspects.
Is it better, regarding the SAP security, to have an internal or external development team?
Read More
Topics:
programmazione sicura,
CVA,
codice sicuro SAP
Is it possible to customize passwords for categories of users? Where and how are passwords managed in SAP?
How can these aspects be checked during an audit?
Read More
Topics:
password policy,
sap password,
secpol
Those areas that are often poorly guarded, when you send emails, may contain sensitive or personal data in the body of the email or in the attachments.
In SAP there is a feature to see all outgoing mails from SAP, also in content terms. Let us see what it is and why it is often underestimated in terms of security.
Read More
Topics:
sap password,
mail security sap,
sost
Do we need days of work every time we have to deal with this issue?
To understand which licenses and how to read the reports extracted from SAP?
Some tips in this article to make the licensing process easier in SAP.
Read More
Topics:
sap license auditing,
audit sap,
slaw,
usmm
What are the main questions before starting a revising project of the authorizations in SAP?
What are the main focus point in a SAP Security Review? How to deal with it and how to be prepared?
Read More
Topics:
documentazione sap security,
SAP Security