
SAP Audit - Vulnerability Assessment - Penetration Test
It’s not at all easy to establish whether a system is secure or not. It is even harder if we maintain it or use it every day.
It’s a little bit like writing an article or a book, all the oversights are difficult to spot if we’re the ones reading it. If we let someone else read it often times these oversights and mistakes are found more easily.
It’s important to have an external point of view that can see anomalies or potential improvements, otherwise impossible to see for those who maintain the systems every day.
Having the awareness that our systems are well managed or have some problems is better than just having no awareness at all
Indice
As said before if we want to have a snapshot of the system current state of health – from a security stand point. It’s always better to know in advance if there are problems, rather than just wait for these problems to show up when it’s too late.
Often times in fact security matters are unfortunately attended when it’s too late. That can be when we were subject to a data-theft or when an internal/external audit finds non-conformities
In these situations, having already run an audit and having fixed anomalies or have a remediation plan can be a strategic advantage.
Why should you rely on a specialized company?
SAP systems have become, as time went by, much more integrated with third party systems and with more functions in them. Their maintenance is often times managed by different actors: the company, external consultants, different companies and with high turnover rate.
All of this has contributed in making the management of these systems complexity much higher.
The skills needed in order to fully understand the possible configurations of security, that go from SAP profiling, to security in applicative configurations, system and infrastructure, and also code, require a lot of specialization.
It’s rare that in a company such specific and vertical skills are found. That is why it’s useful to always have a second opinion by companies that are specialized exclusively in the SAP security field.
How do you choose the company to rely on?
Many different aspects are to be taken into account when choosing a company that will run the audit in your systems.
- Specific company certifications or ISO certifications, in particular ISO 27001
- The ISO 27001 certification requires the passing of specific controls for the secure managing of data
- Vertical focus and revenue stream on the specific area
- How much does a company really work on security? It’s a small percentage of the global revenue or it’s one of the core strategic aspects of the company?
- Employees vs external partner
- A company that is focused on IT security should have a higher percentage if not total, of employees
- Examples of results from audits made in the past
- Insurance coverage
- Case histories
- Is specific software utilized in combination to human evaluation?
Having a specific model or framework can help the presentation and preparation of the results, also making it easier to follow.
Why is the terminology important?
Often times terms like the following are used:
- Security Audit o Security Assessment
- Penetration test
- Vulnerability asssessment
In some cases they are used as synonyms, but each of these means something different.
With Security audit or assessment we mean an examination of systems, with a higher level of detail if compared to the applicative level, given a certain set of rules that are to be controlled. For example:
- Are the systems aligned or does development happen in the production system?
- How many users with critical authorizations are in the production system?
- Are the technical connections between systems protected?
- Are connections protected via the cryptography of the transmitted data?
The number of rules can vary based on the type of audit, and it’s usually defined on the current needs.
Meanwhile a vulnerability assessment (VA) is an activity that focuses mainly on the applicative side, but also architectural by searching for vulnerabilities which are known or unknown. It can be done with the help of specific software and human evaluation. It’s the core value of the service.
It’s important, in these cases, to make how the VA will be conducted very clear. Will only software present on the market be used (open source or paid), or will there be a human component as an ulterior check.
In this case, once a vulnerability is found, no further action needs to be taken. Evidence of its existence is given.
Meanwhile, a penetration test (PT) is an evaluation of the possibility of data theft. In this case the auditor is taking the place of a possible attacker.
Let’s see how a SAP security audit works and what the SAP Security Audit service contains.
How does the SAP Security Audit work?
Once all the preparations and approvals have taken place (together with the stipulation of a NDA), the process can start:
- Sharing of the elements that need to be controlled/evaluated, starting from a pre-defined catalogue but with personalization possibility
- Installing an extractor inside the SAP system, which can be installed also in a pre-production system (the extraction takes more or less 20 minutes. It can also be completely executed via RFC (RFC (sap.com)) (without any SAP software installation needed). In this last case a direct access to the system is needed.
- Once the extraction is complete the elaboration is started
When the elaboration is complete, the results are presented, all in 10 work days.
What happens after?
-
After every evaluation action it’s normal for some remediation to be necessary. These interventions can be done in autonomy by the client or with our support.
In any case a clear list of suggested actions is shared. Every audit tab has the following elements:
- What has been researched. What has been looked for and also the ideal situation on the topic
- What has been found in the system. The result of what is present in the system at the time of the data analysis.
- Comments by who has done the audit
- Which actions have to be taken in order to pass the control
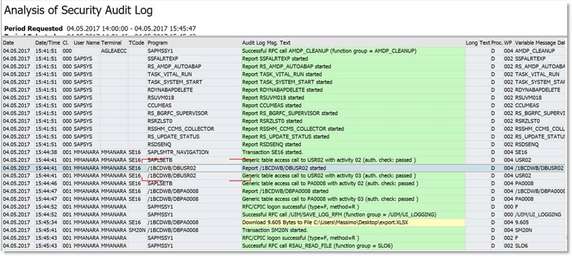
- Attachments that allow a clear view on what the previous information and evaluations are based on, also as support to the findings.
- Degree of criticality
- Normative regulations as reference (for example 231/2001, Legge 262/2005, Legge 300/1970, SoX, Dlgs. 196/2003, UE 679/2016 GDPR– Dlgs. 101/2018 - , ISO27001, ISO29134, ISO29151, ISO9001)
Does it make sense to have a periodic control tool? How should you proceed?
As per their nature, all audit evaluations, VA or PT are subject to obsolescence. Systems are maintained, upgraded, and modified frequently. A more strategic approach has in mind an early audit on the systems, followed by periodic PTs/Vas.
At the end of the evaluation it is essential to correctly put in place all the tools for a constant monitoring on SAP security and plan future evaluation sessions.
Aglea created a tool that allows to keep an eye on the system configurations. In real-time. This is possible by activating personalized alerts that are used to manage the detected non-conformities.
How can Aglea help you?
We’ve been offering SAP systems security auditing services since 2003. We developed a framework of controls (more than two hundred) that are specific for a SAP. These controls not only interest SAP ERP systems, but also other SAP systems (BW, S/4HANA, GRC, CRM, SRM IS-U, IS-M and many more)
We can underline non-conformities, suggesting the needed actions that need to be taken in the system. We can also support the needed changes in the system configuration emerged during the audit in order to successfully close all the non-conformities found during the audit process.
Other doing audits, we also realize Vulnerability Assessments or Penetration Tests in SAP systems
We also introduced an extra specific security audit aimed at custom developments (in the programming SAP language: ABAP) made by the client. This audit is ideal for analyzing the custom code created over time by the client, and not only detecting security vulnerabilities, but also making an evaluation on the code strength, maintainability over time and performance.
Learn more about our certifications (About Aglea - Aglea) and case histories (Case history - Aglea)
Suggested post from our SAP Security Blog
Tables, Roles, Profiles and Authorizations in SAP
SAP contains hundreds of thousands of tables. In some cases the direct access to these tables allows one to retrieve data faster. Below a list of tables for each defined area:
- SAP Roles
- SAP Profiles
- Users
- Authorizations
- Authorization objects



 Are you oriented to buy SAP Governance Risk and Compliance Access Control?
Are you oriented to buy SAP Governance Risk and Compliance Access Control?